Okta Inc
NASDAQ:OKTA

| US |

|
Johnson & Johnson
NYSE:JNJ
|
Pharmaceuticals
|
| US |

|
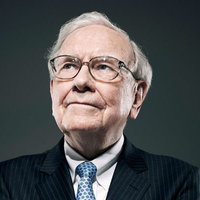
Berkshire Hathaway Inc
NYSE:BRK.A
|
Financial Services
|
| US |

|
Bank of America Corp
NYSE:BAC
|
Banking
|
| US |

|
Mastercard Inc
NYSE:MA
|
Technology
|
| US |

|
UnitedHealth Group Inc
NYSE:UNH
|
Health Care
|
| US |
|
Exxon Mobil Corp
NYSE:XOM
|
Energy
|
| US |

|
Pfizer Inc
NYSE:PFE
|
Pharmaceuticals
|
| US |

|
Palantir Technologies Inc
NYSE:PLTR
|
Technology
|
| US |
|
Nike Inc
NYSE:NKE
|
Textiles, Apparel & Luxury Goods
|
| US |

|
Visa Inc
NYSE:V
|
Technology
|
| CN |

|
Alibaba Group Holding Ltd
NYSE:BABA
|
Retail
|
| US |

|
3M Co
NYSE:MMM
|
Industrial Conglomerates
|
| US |
|
JPMorgan Chase & Co
NYSE:JPM
|
Banking
|
| US |

|
Coca-Cola Co
NYSE:KO
|
Beverages
|
| US |

|
Walmart Inc
NYSE:WMT
|
Retail
|
| US |
|
Verizon Communications Inc
NYSE:VZ
|
Telecommunication
|
Utilize notes to systematically review your investment decisions. By reflecting on past outcomes, you can discern effective strategies and identify those that underperformed. This continuous feedback loop enables you to adapt and refine your approach, optimizing for future success.
Each note serves as a learning point, offering insights into your decision-making processes. Over time, you'll accumulate a personalized database of knowledge, enhancing your ability to make informed decisions quickly and effectively.
With a comprehensive record of your investment history at your fingertips, you can compare current opportunities against past experiences. This not only bolsters your confidence but also ensures that each decision is grounded in a well-documented rationale.
Do you really want to delete this note?
This action cannot be undone.

| 52 Week Range |
71
111.49
|
| Price Target |
|
We'll email you a reminder when the closing price reaches USD.
Choose the stock you wish to monitor with a price alert.

|
Johnson & Johnson
NYSE:JNJ
|
US |

|
Berkshire Hathaway Inc
NYSE:BRK.A
|
US |

|
Bank of America Corp
NYSE:BAC
|
US |

|
Mastercard Inc
NYSE:MA
|
US |

|
UnitedHealth Group Inc
NYSE:UNH
|
US |
|
Exxon Mobil Corp
NYSE:XOM
|
US |

|
Pfizer Inc
NYSE:PFE
|
US |

|
Palantir Technologies Inc
NYSE:PLTR
|
US |
|
Nike Inc
NYSE:NKE
|
US |

|
Visa Inc
NYSE:V
|
US |

|
Alibaba Group Holding Ltd
NYSE:BABA
|
CN |

|
3M Co
NYSE:MMM
|
US |
|
JPMorgan Chase & Co
NYSE:JPM
|
US |

|
Coca-Cola Co
NYSE:KO
|
US |

|
Walmart Inc
NYSE:WMT
|
US |
|
Verizon Communications Inc
NYSE:VZ
|
US |
This alert will be permanently deleted.
 Okta Inc
Okta Inc
Earnings Call Analysis
 Q3-2024 Analysis
Okta Inc
Q3-2024 Analysis
Okta Inc
The company has showcased robust top line metrics indicating financial health and growth, particularly noting a more than 40% increase in the $1 million-plus annual contract value (ACV) cohort. A commendable performance in the public sector vertical contributed to impressive operating profit and free cash flow, signifying efficient business operations. Moreover, the permanent appointment of Jon Addison as Chief Revenue Officer (CRO) and the resolve to continue strengthening the security of the platform underline the firm's dedication to maintain its competitive edge.
In the face of macroeconomic headwinds and a recent security incident, the company expects growth to be impacted, particularly highlighting affected new business and seat expansions. Nonetheless, a 16% growth to $1.83 billion in the current remaining performance obligation, a backlog of subscription revenue expected in the next 12 months, reveals a robust pipeline despite challenges. The company's growth strategy is tempered by an expectation of a downtick in net retention rates in the coming quarter due to macro pressures.
For the fourth quarter, the company anticipates a total revenue between $585 million to $587 million, with a growth of 15%. The projected current remaining performance obligation is expected to grow by 11% to 12%. Non-GAAP operating income is forecasted between $102 million to $104 million. The non-GAAP operating margin is predicted to be 17% to 18%, and non-GAAP diluted net income per share is expected to range from $0.50 to $0.51. For FY '24, an increased revenue outlook along with enhanced non-GAAP operating income forecasts and an improved free cash flow margin outlook to 19% from the previously expected 15%, sets the company up to potentially achieve the 'Rule of 40'—balance between growth and profitability.
The company identifies variability in its products' switching costs due to the diverse depth and breadth of implementation across its customer base. Implementations with numerous custom integrations yield higher switching costs. Nevertheless, despite gross retention rates in the mid-90s, the company is cognizant of the reality that some customer churn is inevitable. The company's approach to a converged platform strategy on both the workforce and customer identity segments bolsters its potential to mitigate such churn and sustain long-term success.





























 You don't have any saved screeners yet
You don't have any saved screeners yet
Hi, everybody. Welcome to Okta's Third Quarter Fiscal Year 2024 Earnings Webcast. I'm Dave Gennarelli, Senior Vice President of Investor Relations at Okta. With me in today's meeting, we have Todd McKinnon, our Chief Executive Officer and Co-Founder; and Brett Tighe, our Chief Financial Officer.
Today's meeting will include forward-looking statements pursuant to the safe harbor provisions of the Private Securities Litigation Reform Act of 1995, including, but not limited to, statements regarding our financial outlook and market positioning. Forward-looking statements involve known and unknown risks and uncertainties that may cause our actual results, performance or achievements to be materially different from those expressed or implied by the forward-looking statements. Forward-looking statements represent our management's beliefs and assumptions only as of the date made. Information on factors that could affect our financial results is included in our filings with the SEC from time to time, including the section titled Risk Factors in our previously filed Form 10-Q.
In addition, during today's meeting, we will discuss non-GAAP financial measures. Though we may not state it explicitly during the meeting, all references to profitability are non-GAAP. These non-GAAP financial measures are in addition to and not a substitute for or superior to measures of financial performance prepared in accordance with GAAP. A reconciliation between GAAP and non-GAAP financial measures and a discussion of the limitations of using non-GAAP measures versus their closest GAAP equivalents is available in our earnings release. You can also find more detailed information in our supplemental financial materials, which include trended financial statements and key metrics posted on our Investor Relations website.
In today's meeting, we will quote a number of numeric or growth changes as well as discuss our financial performance. And unless otherwise noted, each such reference represents a year-over-year comparison.
Now I'll turn the meeting over to Todd McKinnon. Todd?
Thanks, Dave, and thank you, everyone, for joining us this afternoon. We want to kick off this call by addressing what's top of mind for everyone, so we're trying a new format this quarter. In light of the new security blog we posted this morning, we felt it was important to get the earnings release and guidance out before the market opened as well. And around the same time that the earnings press release hit the wire, we posted prepared remarks to the IR website, which contains some of my typical commentary around customer wins and other notable news from the quarter. This new format allows me to spend more time discussing the new information while also leaving more time for Q&A.
I want to start by summarizing the update we shared in a blog post this morning related to the October security incident involving our support case management system. Upon deeper analysis of the event, we determined that the threat actor obtained the contact information of our support portal users across a significant portion of our customers, including the names and e-mail addresses of all Okta admins, except customers in our FedRAMP High and DoD IL4 environments. While this information cannot be used to directly access an Okta environment and does not include user credentials or sensitive personal data, a threat actor may use the information for targeted phishing attempts. With this more detailed information, we felt strongly that sharing this information will help our customers better protect themselves against an increased risk of phishing and social engineering attacks. We have engaged a digital forensics firm to validate our findings and currently expect that they will complete their analysis in mid-December. Once finalized, we will share the report with customers and publicly.
Now let me address what Okta is doing to better protect ourselves from security threats. Over the years, we have dedicated significant resources towards securing our product environment. Given recent events, we recognize that we need to do more to improve the security architecture of our broader operations. That includes the applications we use, the hardware we deploy and the vendors we work with.
Over the past few weeks, we have taken several steps to further strengthen our security posture. We have initiated a hyper-focused security action plan by rallying the entire organization as well as engaging with third-party security firms to fortify our team's efforts. The stakes are high, and we will do whatever it takes to protect our current and future customers. Bolstering our security environment is by far the highest priority for Okta.
The job of securing the Okta ecosystem will never be done, but during this hyper-focused phase, no other project or even product development area is more important. In fact, the launch dates for the new products and features that we highlighted at Oktane last month will be pushed out approximately 90 days. The exception being Okta Privileged Access, which becomes generally available this week.
Now turning to our Q3 results. Top line metrics were strong. We continue to experience particular strength with large customers. Similar to the past few quarters, our fastest-growing cohort was customers with $1 million-plus ACV with growth of over 40%. It was also a strong quarter for new and upsells across our public sector vertical. We also produced record non-GAAP operating profit and record free cash flow in the quarter as we continue to demonstrate the leverage in our model.
In other news, we're thrilled that Jon Addison, who has been our interim CRO since the start of this fiscal year, has been appointed to the permanent position. With Jon's appointment as CRO and our continued confidence in the go-to-market leadership team, we have closed the search for a President of Worldwide Field Operations.
Okta is driven by our vision to free everyone to safely use any technology. The measures we're taking to increase the security of Okta and our ecosystem gives us confidence in our ability to move forward. We will come out of this even stronger because Okta is the only modern platform for neutral and independent identity access management, governance and now privileged access.
Before turning it over to Brett, I want to thank our employees for their tireless efforts. I want to thank our customers and partners who put their trust in Okta every day. I also thank everyone who supported us at Oktane last month, where we had over 4,000 people at the live event in San Francisco and over 19,000 viewing online.
Now I'll turn it to Brett to walk you through more details of our financial results and forward outlook.
Thanks, Todd, and thank you, everyone, for joining us today. The actions we've taken over the past few quarters to drive efficiencies in our cost structure continue to yield impressive results. I'll review our third quarter results and our outlook, but first, I'll start with some commentary on the macro environment. Macro headwinds, while stabilized, continue to impact our business. Metrics that we use to gauge the macro environment such as contract duration, average deal size and pipeline mix were largely consistent with what we experienced in the first half of the year.
Separately, we published the advisory regarding the recent security incident on October 20, which was 11 days ago in the quarter. While business at the close of the quarter slowed somewhat, our overall financial performance in Q3 was strong.
Turning to Q3 results. Total revenue growth for the third quarter was 21%, driven by a 22% increase in subscription revenue. Subscription revenue represented 97% of our total revenue. International revenue grew 20% and represented 21% of our total revenue. FX had a minor impact on total revenue growth but was a 2 point headwind to international revenue growth.
RPO or subscription backlog grew 8%. The general shortening of contract term lengths signed over the past several quarters has impacted total RPO growth. Our overall average term length remains just over 2.5 years. Current RPO, which represents subscription backlog we expect to recognize as revenue over the next 12 months, grew 16% to $1.83 billion.
Turning to retention. Consistent with prior quarters, gross retention rates remained strong in the mid-90% range. Our dollar-based net retention rate for the trailing 12-month period remained strong at 115% and was driven by both upsell and cross-sell activities. Similar to the past few quarters, macro-related pressure resulted in smaller seat expansions than in previous years. We believe this trend will persist in the current environment. The net retention rate may fluctuate from quarter-to-quarter as the mix of new business, renewals and upsells fluctuates. As I've noted previously, we've experienced a macro-related shift in our business mix to more upsell and cross-sell versus new business.
Before turning to expense items and profitability, I'll point out that I'll be discussing non-GAAP results unless otherwise noted. Looking at operating expenses. Total operating expenses for the quarter were lower than expected. The better-than-expected profitability is due to the combination of revenue over-performance and our continued focus on spend efficiency measures.
Total headcount at the end of Q3 slightly increased sequentially to approximately 5,900. Q3 free cash flow was a record $150 million, yielding a free cash flow margin of 26%. Free cash flow was significantly better than expected, driven by billings and strong collections. During the third quarter, we opportunistically repurchased $150 million of our 2026 convertible debt notes. This resulted in an $18 million GAAP-only gain. Over the past 3 quarters, we've repurchased $900 million of debt resulting in a $91 million GAAP-only gain. We will continue to regularly evaluate our capital structure and capital allocation priorities.
Our balance sheet remains strong, anchored by $2.13 billion in cash, cash equivalents and short-term investments. Our cash, cash equivalents and short-term investments position net of remaining convertible debt is $820 million.
Now let's turn to our business outlook for Q4 and FY '24 and a preliminary look at FY '25. As always, we take a prudent approach to forward guidance, we are factoring in a stable but still challenging macro environment. We're also factoring in the recent security incident. For the fourth quarter of FY '24, we expect total revenue of $585 million to $587 million, representing growth of 15%; current RPO of $1.875 billion to $1.880 billion, representing growth of 11% to 12%; non-GAAP operating income of $102 million to $104 million, which yields a non-GAAP operating margin of 17% to 18%; and non-GAAP diluted net income per share of $0.50 to $0.51, assuming diluted weighted average shares outstanding of 180 million.
For FY '24, we are raising our revenue outlook by $30 million at the high end of the range. We now expect revenue of $2.243 billion to $2.245 billion, representing growth of 21%. We are raising our outlook for non-GAAP operating income by $65 million at the high end to $283 million to $285 million, which yields a non-GAAP operating margin of 13%. Non-GAAP diluted net income per share is raised to $1.47 to $1.48, assuming diluted weighted average shares outstanding of 179 million. And we are raising our free cash flow margin outlook for FY '24 to 19% from 15% previously. On a dollar basis, that's a raise of over $90 million and sets us up to close the year achieving the Rule of 40.
While we are still in the early phases of financial planning, we would like to provide a preliminary view of FY '25. I'll reiterate that we are prudently factoring in a stable but challenging macro environment as well as potential impacts from the recent security incident.
We continue to focus on expense control and estimated non-GAAP operating margin of approximately 17%. We're also targeting free cash flow margin to be at least 19%. From a revenue perspective, we estimate total revenue to be in the range of $2.460 billion to $2.470 billion or growth of approximately 10%. We are applying a static 26% non-GAAP effective tax rate for FY '24 and FY '25.
To wrap things up, we are confident that we've set the path of profitable growth for years to come. We continue to focus on initiatives to drive the top line while making significant progress to drive improvements to our operating and cash flow margins.
With that, I'll turn it back over to Dave for Q&A. Dave?
Thanks, Brett. I see that there are quite a few hands raised already, so I'll take them in order. [Operator Instructions] And with that, we'll go to Brian Essex at JPMorgan.
I guess I'll start off with the easy one, and that's the preliminary fiscal '25 outlook. And I just want to ask you in the context of, I guess, taking into consideration 2 issues in particular. One would be the impact, as you guys alluded to, of the most recent breach on your pipeline, close rates, customer relationships. And the other would be, I guess, the need for you to improve your relationship with channel partners in order to drive better growth. So with regard to that preliminary outlook, how should we think about assumptions baked into that outlook, particularly as it relates to traction or churn with customers and contribution from partners considering these issues? And we're in the spectrum of guidance being "kitchen sinked" until we consider this forecast to be.
Brian, thanks for the question, and thanks for jumping on the release this morning early before the market. That was a little bit atypical given the situations of the customer advisory, but we appreciate you covering, everyone else that covered it as well. We know it's extra -- something you weren't planning for us. We appreciate it.
I'll comment just on the business strategy behind the guidance first of all. I think that might be helpful. The -- we have -- it's very important and it's very clear to everyone at Okta that security is the top priority. We've prioritized security at some level over the years, and it's been balanced with other priorities, growth, new product development and various things to run the business. And those efforts, I'm simplifying a little bit but often have gone into product security, infrastructure, making sure that was very, very solid. And we know now that we -- that's not good enough. We have to do more.
We know that Okta is one of the most targeted companies in the world because of the leadership position we have in this important market of identity access management, and that makes us, along with other cybersecurity companies, extremely targeted and relentlessly attacked. And we have to raise our game to be able to defend ourselves and our customers against those attack. So we're really upping the level of priority, and it's very clear to everyone at Okta that, for the end of this year and going into next year, that the #1 priority is securing Okta and securing our customers, full stop. And everything else is prioritized after that.
And the second most -- the #2 priority is -- after security is growth and profitable growth, profitably growing the business. And I think you see that reflected in the business strategy in terms of the direction we're giving teams. We have a 90-day all hands on deck in terms of focusing on bottoms-up ideas and security efforts across the company, getting help from outside industry experts tops down to bolster our own experts. We've done this in various degrees over the years, but we're really aggressively doing more of this to get all the best minds and best input on these opportunities and problems for us.
We're making sure that it's not just of a 1 year or 1 quarter change. It's really a continued accelerated evolution of our cultural change to really being -- having the culture of one of the most secure companies in the world.
Remember, Okta started as a -- it was -- our focus was enabling technology and making it easy to adopt the cloud. It wasn't necessarily started 15 years ago as a cyber company. Now that changed a few years into the company, and it's very clear to us now that -- and has been for the last few years that the bar is the most secure company in the world, full stop. And so that's the #1 priority, and that's what we're focused on.
And then part of that, of course, is kind of the last pillar that we're really focused on now, which is making sure the products themselves, as customers use them, the actual security use cases on those products are prioritized incredibly highly. A great example of that is making sure that when we think about managing access to privileged resources, we -- with our new privileged access management product, making sure we prioritize and make it work great with our own Okta administration console because attackers are going after that because that's such a valuable target.
So it's a wholesale clear communication to customers and to employees and to partners and investors, security is the top priority, full stop, and we will stop at nothing to make sure we become one of the most secure companies in the world because it's kind of clear to everyone that we're short of where we need to be now, and we will fix that.
And I'll just add a couple of comments there, Brian. Thanks for -- one, nice to see you. Thanks for the question. But in terms of the guidance philosophy, really no difference from what we've done before. I think we all know, for years now, we give this early look. It's a prudent look. We've got 5 quarters ago. We've got a big Q4 ahead of us. And so we're factoring in 2 major factors, like I said a few minutes ago, which is around the macro and then also around the security incident and making sure we're being prudent about the guidance at this point given how far out we are from the end of FY '25.
On the -- you asked a question too, Brian, about the channel partners?
Yes.
I think that's -- I would say that's a continued thread and a continuation of what we've been doing this year with our enhanced partner program and clarifying the partners we're working with and investing on the ones that are really moving the needles. The things you've heard us talk about in previous calls, that's an ongoing thing, and we're continuing to execute on that and seeing benefits from that in the business.
I guess do you get the pipeline internally to hit that number without incremental improvement in partner contribution? Or how confident you are doing that [ 10% ]...
We're very happy with where the pipeline is.
Yes. We're confident in what we've given you guys today. Like I said, no change in the guidance philosophy.
Let's go to Rob Owens at Piper.
I appreciate the transparency and disclosure around the breach and realizing these things can take on a life of their own as time passes. But I was curious more so what you're doing for customers to assuage concerns around the breach itself aside from pushing out some launch dates here. And any proactive steps that you're taking to help future retention?
Yes. I've been -- I've had many, many conversations with customers over the last few weeks as you can imagine, and the reactions vary. Some are from, "Thanks for the update. We appreciate the communication," to the other extreme, which is a lot of frustration and concern. The common thread or the common theme is that we're incredibly important to our customers, and they're relying on us for their critical infrastructure of their Customer Identity or their Workforce Identity. So it really matters.
And the first thing they want to know is that do we know how important this is and are we taking these things seriously. Do we have the right plan in place to react to these things and get better going forward? And when I talk to them, the themes that resonate are really clear priority, comprehensive look at all the threats and all the opportunities across product and infrastructure, making sure the cultural tone from the top is set appropriately, and I can do that in a way no one else in the company can do. So I'm very clear about that.
And then the last thing I talked about before is how the products can help them be more secure because this all is about the foundation for their security. And once that foundation is solid, then they can use our products to be -- to further enhance their own security.
So I think to your specific question about what we're doing specifically, I think it's -- part of it is being open and transparent. One of the reasons why we thought this most recent disclosure, the one we did yesterday and then publicly this morning is that when we talk to customers, the #1 thing they want is transparency. And they want to know as soon as possible what is the risk increase, what are the threats. And our commitment as -- on our journey to be one of the most secure companies in the world is to make sure we fulfill that commitment and make sure we're open and transparent and disclose all the information we have.
So I know it seems a little strange right now, but in some ways, what we did yesterday and today are executing on this plan and this commitment we've made to them. And then I think there's many more things we can do in terms of just making sure customers understand what happened and what we're doing about it, and you'll see us do more about these -- toward these communication efforts going forward.
But at the end of the day, I was talking to -- I have -- I was talking -- one of my conversations was with a CISO of a large manufacturing company that's been heavily adopted on Okta, and this is common to how these things go. He said, Todd, this -- you are -- the position you are in the ecosystem in the industry, you are one of the most attacked and focused on from an adversarial perspective companies in the world. And we know that if you take this as seriously as you're saying you do and you have these plans and these priorities in place to improve your -- make sure you're one of the most secure companies in the world, that's going to be more than enough for what we need because you're going to be attacked way more than we ever will.
And so I think they see it as -- once we communicate the details, once they can understand our plans and our priority and our focus, they come away with more comfort. But again, at the end of the day, what they really want is no issues like this, and that's ultimately our goal, to try to prevent these whenever possible.
Let's go to Adam Tindle at Raymond James.
Todd, I wanted to ask a little bit more about the renewal process in light of the security incident. Brett mentioned that contract duration continues to shorten, so the thought would be the renewal process is likely happening more frequently moving forward. Wonder what kind of processes you have in place to retain customers. And any ideas that Jon brings to the CRO role to this process? And Brett, if you could just touch on the assumptions on gross retention and NRR embedded, I know you're factoring in the security incident, but I would imagine that's where it's going to hit the most, so that would be really helpful to understand what the assumptions embedded are.
The renewals process and execution of that is something where it's a very mature part of our company and we're very good at it. I think it leads to our -- as we've talked about several times, the gross retention in the mid-90s is a healthy level. And it's -- so it's a strong muscle we have.
Contract durations, as Brett mentioned, have been shortening. I think it's -- they're still, on average, 2.5 years. And the reason they're shortening is this started happening during some of the more economic slowdowns last year. It's just, I think, across the board, people are not signing up for as much as they -- in terms of length of subscription as they wanted to.
So I think that the renewals conversation will continue to be addressed effectively by our existing motion that we don't need some kind of new motion or new conversation. I think it comes down to making sure that the adoption of the product is high, which we're very good at getting our products adopted and making sure that the value is being delivered and that the price they're being charged for is fair. So there'll definitely be some -- as we just communicate to customers about our prioritization of security and our focus on and our execution across that plan, that will be funneled down to the renewals team as well. But I don't see any big changes to the overall renewal motion because of this.
Yes. I can also add on to that, Adam. Thank you for the question. So first on the contract duration, just to be clear, there's been a general shortening of contracts to what Todd was talking about, but part of the reason is actually the success we've had in public sector, which typically is only a 1-year contract. So that business doing well is going to put a headwind on our contract duration, so I guess, that's a good issue to have in terms of contract duration.
So in terms of what we baked into the guidance for specifically NRR, net retention rate, or gross retention rate in FY '25, we haven't gotten to that level of detail given we're so early in the planning process. But what I would say is we do believe both the macro puts a headwind on growth and also the security incident. And so where each of them comes through, I mean, macro, we've talked about new business, seat expansions being impacted there. From the security incident perspective, we think growth is impacted. I can't give you exactly is it more upsell or is it more gross retention in terms of FY '25.
But what I can tell you is, in terms of FY '24, like we've talked about in the past, we did expect that number to tick down. Net retention is going to tick down throughout the balance of this fiscal year. And we had a nice quarter in Q3, 115%, flat with Q2. So we do still expect it to drop in Q4 based on those macro headwinds we've talked about with seat expansions but that hopefully helps you with a little bit more detail on how we're thinking about FY '25 as well as that net retention rate in the very near term next quarter.
Next go to Rudy Kessinger at D.A. Davidson.
Appreciate the candor as it relates to the breach. Todd, at Oktane, it seemed pretty clear that you were hinting that you guys were close to hiring a new President of Worldwide Field Operations or Head of Sales, and today, I know you're closing that search. You're moving Jon into the permanent role. So I guess I have just a couple of clarifications. Did the breach impact your ability to land a new Head of Sales at all? And secondly, just understanding the current structure, is Jon going to be taking on both the Head of Sales and Chief Revenue Officer roles? Or will you be remaining, I guess, the Head of Sales for the time being?
Yes. Thanks for asking for clarification. On the previous question, I forgot to answer the part about Jon. The decision for the go-to-market structure was finalized before October 20, so it was finalized in early October. So it had no -- nothing to do with the security incident. The -- I think there were -- since the search started in January of this year, late January, the time line on it was we were going to make a decision to finalize things by October, and we hit our time line.
So we didn't want to have an interim structure going into planning for FY '25, so the goal was to finish it by the end of October. We -- I can't remember exactly the order of operations in terms of when the final decision was made versus when I made those comments. But what I knew at the time for sure is that we were going to finalize one of our finalist candidates and Jon being one of those finalist candidates. We were going to finalize it soon and be ready to roll on our original schedule, which was, like I said, to wrap it up in October.
The decision came down to a few things. One is that the -- I think that Jon is -- I talked to dozens and dozens of candidates and interviewed and looked everywhere and different levels of experience and backgrounds. And every person I talk to, the person doing the job was outperforming them. Jon was doing a great job. I was with him in customer meetings around the world. I was -- more importantly, talking about strategy going forward and understanding his strategic vision and his familiarity with the market and areas around the world and with the product segments and the identity industry and he would just really shine brightly. It's like the 9-month job interview.
And it really -- it kind of made it hard for other candidates to compare. And I think -- so once I made the decision that he was the right guy to be the Chief Revenue Officer, I also made the decision that I really like the current structure of business operations under Eugenio as the President of Business Operations -- Global Business Operations; the marketing function under one of our strongest operational executives, Eric Kelleher; and then Jon running sales and presales and partners reporting directly to me. So basically, the flatter organizational structure where I have direct the business operations, customer success or customer -- Chief Customer Officer marketing and then Chief Revenue reporting directly to me, it was the best thing for us going forward.
So there's really like 2 decisions. It was who's the best Chief Revenue Officer in the world, and then do we need that extra layer of a president. And the best thing for Okta for the future is to finish out the search for president and have these talented capable people in place that drive us forward.
Great. Let's go to Hamza, Morgan Stanley.
Todd, on a high level, could you speak to the switching costs of your products? And based on your very early conversations, would you anticipate some customer churn as a result of the incident?
I think the switching costs vary and it's one of the great things about both the Customer Identity products and the Workforce Identity products, are that you can -- they're very flexible. You can implement them very quickly and easily. And then you can also implement them in a way that's quite comprehensive and connected to everything and very complete and cover every technology and every resource in the customer's environment. So the switching costs vary.
I mean there are companies that have a relatively light implementation and the switching costs are pretty low. And then there are implementations that are very deep and broad and lots of custom integrations and so forth, and the switching costs are higher. So I think it varies.
I don't -- I think there's various reasons why people switch off. And I think it's pretty hard, and it's always in customers that are less likely adopted and have lower switching costs, which is -- seems pretty obvious, but that's true. And I think that -- I think we're -- we've seen some people switching off for various reasons. Sometimes it's -- like we've said, our gross retention is mid-90s, but -- so that means, by definition, there's some percentage that are switching off. Various reasons for doing that. And I think at the end of the day, it's going to be hard to directly ascribe it to one thing, so I think we're just trying to make customers successful and provide huge value in the products.
And our strategy of a converged platform on the workforce side and covering every identity use case with customer and workforce. And we have, I think, prudent assumptions in the forward guide about what is baking in security incident or baking in macro. We're comfortable with that guidance, and we're going to go out there and execute our plan. And I think it's going to be -- in the long term, we're going to show a lot of success and deliver a lot of value to customers, and that's going to drive success across the board.
We'll go to Joe Gallo at Jefferies.
Impressive margin performance this quarter and guidance next year. Can you just further unpack the drivers of leverage there? And then just talk through whether that inhibits the growth algo at all. And then just maybe whether -- how do you think about longer-term growth? Do these margins kind of reflect a new reality of potentially a lower long-term sustainable growth?
Thanks, Joe. So in terms of the -- how we're achieving this, this is really something we've been working on for probably about 18 months at this point. I don't know if you remember. Last year, we started this cost structure efficiency whether it be from moving headcount to lower-cost regions or rationalizing software, rationalizing real estate. It's been a long-time effort for us to be able to really set up the structure to be able to deliver these types of margins.
I'm really excited that actually we can talk about Rule of 40 this year because that's how we look at the business and manage the business and kind of think about it from the lens of growth versus profitability. But ultimately, all this hard work is allowing us to offer up and guide with confidence these margins that you see in the FY '25 guidance, 17% non-GAAP operating margin, at least 19% free cash flow margin.
And so that's a really good shift for us. We've set up that structure to be able to drive that efficiency, drive the leverage in the business. And as far as growth versus margin, we're always going to balance the 2 and ultimately look to balance the 2.
So I can't give you anything beyond FY '25, but we're always going to manage the business through that lens of the Rule of 40, something we're very proud of that we feel we can achieve this year and we'll always target as we as we move forward into FY '25 and beyond. It's something we really kind of pride ourselves on doing overall.
Next up, we're actually going to go to Madeline Brooks at BofA. She got knocked out of the queue. I'm putting her back in the spot here.
Appreciate it. And just appreciate the transparency of your remarks. I know many people have said that, but just really want to emphasize that.
So the question is if I look at what happened this quarter, my quick math implies that roughly 99% of net new cRPO came from the existing base. It's a two parter. Across peers, those numbers begin to kind of turn positive again, where contributions from net new customers increasing post macro. So the first part is why do you think the trend in your numbers is different than other cyber peers. And the second part is, is there any concern that heading into next year, the existing customer base will already be saturated leaving less room for upside, especially with this 90-day pushout of new products and the potential headwind from the new bids given the recent security event?
Sorry, Madeline, you broke up a little bit on me, but I think you were saying the mix on cRPO was related more to upsell versus new business? Is that...
She said she calculated 90% of the cRPO came from existing customers.
Yes. Okay. Yes, I can't say that I have that number at hand, Madeline. But what I will say is, as we've talked about in the past, our mix of business has shifted more toward upsells. We believe that's related directly to the macro side of the house really putting pressure on new business, and so I think that's why you're seeing those numbers.
I think we had a nice quarter from new customer adds. Net adds was up 400. You heard Todd talk about the $1 million customers. Greater than $100,000 customers had a nice addition as well, an increase sequentially versus Q2. So we do see new business helping us out, but we do see a headwind there due to the macro headwinds that, although have stabilized, still are headwind to our growth in the business.
Yes. And one thing I can add there, hopefully, it's helpful, is the new products. We have with -- we have 3 amazing products to sell our existing customers. I mean some customers have Customer Identity, but we still have a lot of customers to sell Customer Identity to. And then we have many, many customers to sell Okta Identity Governance to. That thing is just starting to roll. It's had some early success, but it's been GA-ed a little over a year now, starting to get a ton of traction. We had a couple of really important deals with the one I mentioned in my comments that we posted at the site, was a global pharmaceutical company, had a big OIG upsell and then the new GA of PAM.
So I don't -- I think we have a ton of new products from the pipeline to sell our customers, and that's what we're making sure we operationalize those newer products and execute well in selling those. And I think the 90-day delay on some of the new products could potentially be impactful at some point, but we're not short of products for FY '24 for sure -- or sorry, FY '25 for sure.
Let's go to Eric Heath at KeyBanc.
So Todd, it's great to see PAM's getting rolled out this week. I guess kind of 2 parts to the PAM opportunity. So one, just what learnings can you draw from OIG to relay that into some similar early success into PAM, number one? And then number two, just given PAM can be used to protect the customers on Okta environment, is this something that you could potentially make available to customers at no extra charge just as it relates to protecting their own Okta environment?
I think there's -- we're really excited about Privileged Access. And I think the biggest -- I think there's a couple lessons from OIG that are just -- I would call them independent of any product area, so just new product introductions across the board, things like best practices to when to enable broadly, when to enable different segments of the market. Like one of the learnings from OIG was that it's having much more success in larger enterprises than we expected, and so I think we'll roll that learning to PAM and will enable the larger enterprise sellers sooner than we did with OIG because we anticipate that it could have the same phenomenon and exceed our expectations in larger enterprise.
Another interesting phenomenon for OIG was that OIG is exceeding our expectations in kind of, call them, brownfield environments where they already have an existing governance solution. So we'll bring those learnings to the PAM product as well.
On the product direction, one area that is -- through the early access phase and now that we move into GA, one of the learnings on the product directions is that customers -- the product's main focus has been through the LEA, Limited -- or sorry, through the early access has been on servers, so Linux and Windows servers, Kubernetes clusters, managing access to these things, these kind of infrastructure-type resources.
Customers find a lot of value in having us manage the privileged accounts in SaaS apps. So we're connected to Salesforce. We're connected to Workday. We're connected to GitHub, manage the privileged accounts in there. So that's an exciting direction as, as you mentioned, what is one of the most critical privileged account systems in the world. It's Okta Admin Console.
So we're exploring ideas to better integrate that, and that's going to be a big focus. And your idea about offering it for free to every Okta customer is a very interesting one. And this might be the first time ever I've taken product input on an earnings call, but I do take it.
Great. Next, let's go to Gray Powell at BTIG.
Okay. Great. So yes, I guess, kind of a modeling question here. Normally, I would expect sequential growth in cRPO in Q3 to be at a similar level to that of what you've seen in Q2. At least that's what you've seen the last couple of years. This year, you added $54 million in net new cRPO. Last quarter, you added $71 million.
So I know this is kind of rough. But like is it safe to say that the main difference there was the breach happening with like 10 or 11 days left in the quarter and then customers just taking a pause? Or is there something else that I should be thinking of?
And then the other part of the question would be, as we think of Q4 trends, like how much of a hangover is there? How much should we expect the lingering impact of the breach to be on conversations with customers?
Yes. Thanks, Greg. So from a sequential perspective, I think I wouldn't do that math in terms of backing into the impact associated with the incident. I would more think about renewals timing. That can have a heavy impact on cRPO quarter-to-quarter. So we feel we had a really nice quarter in terms of Q3 growing 16%, $1.83 billion in current RPO. So I wouldn't read too much detail into that.
In terms of Q4, all of it's baked in. All of what we think the potential impact is associated with the security incident, that is in the guidance that we've given you here today, 11% to 12% and $1.88 billion at the top end of the range. So that's kind of how we think about things.
Go to Peter Weed at Bernstein.
It looks like the change in your anticipated growth in quarter 4 came down relative to what you implied last quarter by almost 3 percentage points. And I think you've said that this is the impact of the outage. Is that experiential? In other words, like there are some things that you've already seen occur that are leading you to believe that you will definitely see that.
And is that turning up in customers that are kind of showing that they're going to leave? Is that people are failing to upgrade at the pace that they have been before? Is that it's harder to win new customers, so you anticipate -- you had a really nice quarter actually, getting new customers, sequentially up. Do you anticipate that to take a dive? I'm trying to figure out like where that shows up kind of in the stack of where you would have normally thought that kind of sequential growth quarter-over-quarter, that seems to have been kind of eliminated as a result of the outage.
Yes, the incident. So if you look at every quarter, Peter, there's always deals that push from quarter-to-quarter. It's just a natural part of our business. We saw an elevated level of that, and we ascribe that, that potentially could be related to the security incident. So we're taking that into our guidance when we think about Q4 and thinking about it from a prudent perspective, especially given how big the number can be in Q4 and setting the trajectory for fiscal year '25. So that's how we're thinking about things.
So it's actually more just there are deals that stayed in the pipeline, but you just anticipate they may push out of this quarter into the next quarter. But they [ did ] already from Q3 into Q4. Wouldn't that like give you deals that would be closing in this quarter that should plug some of that gap? So you'd have to really push out a lot of deals out of Q4 and to Q1 at that point.
Yes. And you're right. We actually have already seen some of those deals close in Q4, which is a good sign, but we're being prudent given the environment out there today, given both the macro and the impact associated with the security incidents. So we're just being thoughtful.
Yes. I mean if you think about the chronology of it, it's 11 days left in the quarter, and then we're only just a month into the fourth quarter. So we -- in terms of the window to see the impact, we're a little bit limited on a window to see the impact, so I think that drives some of the pragmatism in the guide.
All right. Let's go to Adam Borg at Stifel.
Maybe a bigger picture question here. So international is still about 20%, 21% of the mix. And just given the size of the company, just seems like there's a lot of international opportunity ahead. So just as you think about the channel investments and you think about the new CRO and CMO in place, what are the thoughts about kind of accelerating opportunity in the international theater to potentially help accelerate growth?
I think it's a big opportunity. I do think from a macro perspective in terms of the stabilized macro but still a challenging macro, I think the macro impact internationally has probably been more pronounced, from my observation, than in North America over the last year or so.
We also have -- in terms of the interim to permanent CRO with Jon, that also gives us the opportunity to backfill Jon as the General Manager of Europe, and we have some candidates in the late-stage pipeline for that. So that's more leadership stability internationally. Couple that with a great leadership team in Asia Pacific, which is performing well. You have a really good opportunity for solid performance internationally, which is -- has to be an important part of our future.
If you just look at the numbers, the market is -- half the market's probably outside the U.S. over time in terms of identity management. We're using rough numbers. And over the next 5 to 10 years, we're going to make sure we get that mix higher than it is now in terms of a percentage of revenue.
I'd also add, just Jon being an international person himself, like he brings that lens, right? And so we're really excited about that and the opportunity out in front of us because I agree with Todd. We've got a lot of opportunity internationally.
Next up is Matt Hedberg at RBC.
Great. Todd, a product question. In your prepared remarks, you noted you're pleasantly surprised, I think, by the size of organizations adopting your Identity Governance product. I think a year ago, it probably would have surprised a lot of us. I think we would have thought maybe some of the traction would have been from smaller organizations or midsized organizations.
So I guess maybe why the success up market, do you think, at this point? And then, Brett, when you think about the impact to -- from governance in your '25 outlook, I assume you're taking a very modest approach. But just thoughts on how you're thinking about that product next year?
The -- I just think that large organizations have -- there's a lot of complexity. And I think maybe we underestimated the -- I think we looked at some of these larger organizations and what they were doing with the existing governance solutions, and we assume that they were -- these solutions were covering the SAPs, the Oracle apps, the legacy apps and assuming that they would also be covering all the cloud stuff and all the new. I think that assumption is just proving to be maybe not as accurate as we thought. I think a lot of these legacy products aren't covering where the center of gravity is moving, which is cloud-centric application workloads and cloud infrastructure. And so the product is a better fit for these large companies than we thought.
I think also just our overall -- the last, call it, 5 or 6 quarters with -- when the macro environment changed, you're just seeing more success for Okta in the bigger companies, so I think it's -- I think OIG has a big future in mid-enterprise and SMB. But I think that segment is just the slower segment right now, so we're not seeing the attaches with OIG there that we could over time.
So I think your -- it looks better because more people are -- have the problem and finding value from it in a large enterprise. And also large enterprise is just doing so well with 40% growth in that cohort, both in ACV of those deals and in customer kind of those deals in Q3. So I think attaching OIG -- there's more opportunities to attach there relative to the entire business, so I think that's influencing the perception as well.
Yes. And I would add, although we're very excited about the progress so far, Matt, I mean, yes, we are being modest with our expectations in the guidance we've given you here today. One thing that I know you guys have asked in the past is how much -- and we've told you -- we keep telling we're going to update you every time we get a new number. But that third of workforce spend being IGA continues to hold steady through the end of Q3. So that's the number we've given you in the past, and it continues to be that. So the upsell associated with it is significant, and we're very pleased with how things are going just like Todd said.
Great. Next up, Jonathan Ho at William Blair.
With regards to the breach, can you give us a little bit more detail on maybe what's still left in the third-party validation and investigation? And how confident are you that this is going to be the last finding that comes out of this investigation?
Yes. It's a great question, Jonathan. In my many, many conversations with customers, this comes up like speed of disclosure, and they want to know all the information as fast as possible and why does disclosure take time and what else is left to disclose, et cetera. So it is on everyone's mind obviously.
I think the general philosophy we're taking is that we're trying to disclose as much as we know as quickly as possible. I think a couple of weeks after the incident, when we had our first disclosure, we disclosed everything we knew at the time. And we just kept looking.
Like you're talking about the log files from our support system. We're quite voluminous, and the team went over them click by click, row by row, line by line, kind of took first pass and looked at all the things they thought were incredibly sensitive and took a quick run of some of these reports and found it wasn't much interesting data and then published the first RCA and remediation steps and then like a good security company would, kept looking and kept digging and made sure we had everything covered and far more. And we were more thorough about these reports and ran completely and saw the data was there, made the decision to do a further disclosure based on risk of phishing like we've outlined.
And so I think the way I characterize it is now our internal team has gone over it many, many times, and our internal investigation is done. Like we don't think there's anything else productively we can look at. We've worked with the vendor and got supplemental logs. We've combed through it. We've done everything 3, 4, 5 times to check it. But we still want to make sure we cover all the bases, so we brought on this firm that has started a couple of weeks ago, and they're looking at it.
I think we're doing it, obviously, to be very thorough and clear. I think it's a relatively low priority that they'll find anything additionally, but we'll have to wait and see in mid-December when they're done with their analysis.
Okay. I'd like to welcome back Fatima Boolani from Citi.
I appreciate the question. Todd, you were very categorical about securing Okta. So your customers are secure as being the #1 priority. So the question for you is, is that a people, process or technology or maybe all of the above conversation. And then maybe, Brett, it's not immediately apparent in your margin guidance that you're going to be taking and making these investments. So can you just sort of help us understand and kind of what envelope a lot of this up-leveling and reinforcing of your internal security architecture, what shape or form is that going to take?
Yes. It's a super insightful question, Fatima. The -- it's -- and as you guessed, it's all of the above. And I think we -- the program internally is called program bedrock, building the bedrock foundation. And it has 4 pillars. I'll call them pillars.
The first one is there's just bottoms up get all the ideas on the table of everything we know that the team thinks would be great ideas to make us the most secure company in the world. And like a good example of something from this pillar is like this thing that we're advising customers to do with the latest notification around having MFA for all administrator accounts. That really should be required. There shouldn't be an option to not.
Again, over the years, we, in some cases, made the choice for convenience and speed of implementation or frictionless adoption instead of security. But as we march toward being the most -- or one of the most secure companies in the world, that's going to change.
So we have to make that required and you got to work through that because there's a reason sometimes customers don't have MFA required. Maybe it's a service account. Maybe there's a specific workflow. But everyone, as we do this bottoms-up effort, it's like a lot of good ideas on how we can make that better.
And that whole bucket of bottoms up, we have a lot of awesome smart people on the team that have the time and space now to let those ideas come out, and they're going to -- we're going to have time and space to implement them as well. So that's the bottoms-up track.
The second track is really, call it, tops down, which is making sure from an internal security architecture perspective, specifically in overall business operations and IT operations as inclusive of obviously product and infrastructure, but getting the top experts in the world and to give us their opinion on how we should be architecting our -- this part of our security posture and architecture, and there's people that do this for the most secure companies in the world, and we want to take those experts and combine them with our experts internally to make sure we have the best security blueprint from an architectural perspective. So we have bottoms up. We have tops down.
And then the third pillar is really cultural. And that starts with me and the leadership team in setting this clear priority and setting the expectation that we are going to be the most -- our goal is to be one of the most secure companies in the world, and we're going to prioritize that, number one.
When you think about executing well, it can be pretty straightforward. It's like you have to make sure you have a clear vision. We want to be one of the most secure companies in the world. We want -- you got to set clear priority and get the right amount of resources on it. And that kind of sets up this cultural component to be successful.
And then the last one is, I think I mentioned before, is in the product. We have to make sure that the products themselves are beyond just being valuable and powerful for our customers. They have to be built in a way that ensures the security of our customers as well. And the best example for this is, after the notification of this incident in October, we quickly implemented this feature, which actually cryptographically binds an administrator console session to a specific network. So this is the kind of thing that is very valuable for customers and keeps them occur.
And as we think about it more and go through the entire product architecture and overview, there's many more of these things that can put us closer to being, from a product perspective and products that protect our customers and their use of it and their deployments of it, the most secure company in the world. And that's the fourth pillar.
So it's quite comprehensive. The -- I think the 90-day focus gives everyone's space and clarity to have no confusion about this being the priority. And I think after 90 days, what you'll see is obviously these kind of efforts have -- they've been going on in some shape or form for many years, and they will continue after these 90 days. But right now, we just need this real clear alignment on getting ourselves closer to that goal of being the most secure company in the world.
And then for the second part of your question, Fatima, it's -- really, there's 2 things. One, we're already investing a good amount in FY '24. So to step up in the margins, it's not like we're starting at 0. So we're investing a good amount right now. We're going to invest more in Q4.
But this is 1 of the benefits of the structural efficiencies that we found and driven over the last 12 to 18 months. It allows us to expand the non-GAAP operating margin from 13% to 17% while also investing more into these critical areas like security. And so we've invested a lot already. We're going to invest even more in FY '25 but while also being able to balance it with the margin that you mentioned. So it's one of those benefits of us doing what we've been working so hard on for the last 12 to 18 months.
Okay. We're going to try to get to a couple more. Let's go to Josh Tilton at Wolfe Research.
Can you hear me?
Loud and clear, Josh.
Great. I wanted to clarify a previous question. Does the guidance for Q4 embed some conservatism around the recent incident because you are anticipating to see something or because you are already seeing an impact. And then just a follow-up is, Todd, you mentioned that you spoke to customers and they kind of understand why, as an identity provider, you guys are being targeted by hackers so much.
Is that raising any questions from the customer base as to whether or not it makes sense to go all in with all of your identity needs from one provider? Or given that you guys are the center of the security ecosystem and the #1 target for hackers, does it maybe make sense to diversify some of your identity risk across a different PAM vendor and a different governance provider?
Josh, I'll take the first part. So anticipating is the answer, short answer since we're running out of time, because we did see, like I said earlier, an elevated amount of pushes or deal pushes from Q3 into Q4. And so we're just anticipating that as we go through the quarter because, as a reminder to everybody, we do not have a linear bookings quarter. It is very back-end weighted. And so we're just taking into account what we saw at the end of Q3 and looking and making sure we had put that into our expectations for Q4.
Yes. And on the question on the -- getting everything from 1 vendor versus spreading out your risk with different vendors, I think it comes down to -- at the actual physical layer of how the products are implemented, how you mitigate that risk of getting everything from one vendor.
And then the second thing is the product, there has to be a lot of value in getting it from one vendor like in terms of decreasing risk, the operational simplicity, the power of how you can secure things because things are better integrated. So that's the -- in fact, I was having this exact conversation with a customer just a few days ago about the risks and reward of consolidated around one vendor versus the spread things around, spread the risk perspective. And I think that's the -- those are the variables in the equation that people think about.
Go to John DiFucci at Guggenheim.
So Todd, my question is a follow-up to Fatima's question. I got to remember to try to get ahead of her because she -- it's hard to follow her, but I thought that was a really good question. And thank you for all the detail you gave around that, the program, bedrock. But in the end, still like how long is it going to take to get to, as you say, raise your game to get to a point of, I don't know, you're never going to be comfortable but relative comfort when you can actually sit down with the customer and tell them that you're there? You're never quite there, but you're there don't -- listen, we worry about it every day. We don't want this to happen ever again. That's not to say it never will. But how long do you get to a point where you have that relative comfort through that?
Yes. It's a super smart question, super smart question. I think I would add color this way. This has been something we've been very focused on for several years, particularly since Lapsus$ breach a couple of years ago. We've been very focused on it and actually made quite a bit of progress to make us feel comfortable about our progress toward being one of the most secure companies in the world.
I think the reason for the 90-day sprint and focus are as -- there are -- there is a calculation of I and the management team think that there are enough things that will decrease the risk at a significant level. Not that the risk is incredibly high, but there's enough things that'll decrease the risk at a significant level that we think it's worth a sprint here. But probably more importantly, John, it's kind of cultural.
It's execution requires clear priority, and nothing makes the priority clear for everyone than a full focus in a 90-day sprint. So beyond the decrease in risk and getting us closer to this area, as you described it, where we feel real comfortable as we progress toward being one of the most secure companies in the world, there is just a cultural tone setting thing, which I think is very important for customers and for investors and for employees as well.
So it's the 90 days and then just keep going. And by the way, I'm just going to...
And it's not like we've never been focused on security because we've absolutely had a huge focus on it. Like I said, very, very specific and mature in the areas of the product and the infrastructure. I think we're not as mature and we haven't had the comprehensive approach on the overall IT operations and overall company operations. But it's something we've been doing for a long time, and we're going to have the sprint and then we'll keep doing for a long time after because we have to be -- like I've said it many times, we have to be one of the most secure companies in the world given the position we're playing and the critical role we fill for our customers. And that's what they expect from us and that's what we expect from ourselves as well.
And listen, I just have to add one last thing, something I never say. Actually, I think you guys did a good job. I mean this quarter, numbers look good and then even some -- given everything that's going on, I guess, nice job.
Yes, appreciate it. A lot of hard work from the team.
Great. And now we're going into overtime here. We're going to take Fred and then Shrenik, and we're going to have to cut it off at that point. But Fred Havemeyer from Macquarie, go ahead.
I think many good questions have been asked. So I think, Todd, what I'd like to ask is, as we from the outside are looking at what you were doing at Okta, what sort of concrete checkpoints might we expect to see to understand what progress you're making here towards improving your overall security posture, understanding also that no news is kind of good news with respect to data breaches. And secondly, on that one, with the upcoming SEC disclosure time frame and requirements, do you feel that you have the reporting frameworks in place to comfortably meet all of those requirements?
Yes. On the second question, I feel really good about that. The disclosure frameworks and so forth, something we -- I think, in some ways, we're -- the role we play in the industry and the tone and the transparency we're trying to set with customers, we have a lot of things in place that put us in good standing there in terms of our ability to execute on those disclosures.
The first question you asked is I think there's -- for -- we're -- we have a really good answer on the product visible things. We're going to be reporting those out like as we would do product releases or future capabilities. These -- like the 2 examples I mentioned are the network binding for session tokens and the required MFA. That's going to be published. And so you'll see the road map for those things, and you'll see that thing published publicly into customers.
I think the internal stuff, the things that the team comes up with in terms of improving our operational security and comprehensive look at the security and taking in outside experts, we have to think more about how to communicate that broadly to customers. But I think it's just as important because not only is it just give customers confidence and how seriously, how aggressively we're taking this, but also it can help them learn because every customer I talk to, they're thinking like what can we learn from Okta because Okta is on this journey to be one of the most secure companies in the world. I can learn from that. So I think there's value in sharing that not just from the da trust perspective but also from the learning and the helping customers through that education.
Okay. Last question to Shrenik Kothari at Baird.
Appreciate the transparency, Todd and Brett. Just to follow up on your point, Todd, on product security focus and customer security focus. In light of the recent hack incident, I know the role of PAM seem to be elevating and becoming even more kind of broad-based. It's great to see that you guys are focused on PAM, as you said, the only product whose GA is on track versus other product features maybe relatively deprioritized.
Can you elaborate how are you positioning PAM in your customer conversations? More importantly, how are customers responding? And how does the customer feedback evolve? And given post this hack incident on one hand, of course, everybody knows PAM is going to be a key piece of puzzle in this threat landscape, while the incident perhaps leading to customer perception of perhaps not adequate implementation of core PAM solutions within your internal environments on the other hand, so if you can provide your thoughts there, you should.
Yes. No, it's a good -- I think every specific incident is different, and PAM and the definition of PAM addresses some of them better than others. So I won't comment specifically on this recent incident and what our PAM product does or doesn't do. But broadly speaking, what you're saying is right. All of these attacks, whether it's -- are highlighting the need for very strong phishing-resistant access management, identity governance and then privileged access management and control.
And I think the reception that we've seen with customers is, basically, it's very simple. Our position is very simple. It's like you're using Okta to manage the user life cycle and the access for many business applications, you should use the same engine and the same access control for your privileged servers and containers and as I mentioned earlier, in a future release coming relatively quickly for your SaaS applications and for the Okta Admin Console itself. So that's the pitch.
And what customers like is that they get this comprehensive integrated workflow across all of the access points they're trying to secure, whether that's servers, apps, business applications, different kinds of applications, and that's what resonates. And then they can report that back to their auditor, and they get complete visibility from a governance, risk and compliance assessment, and that's the value prop for them.
So it is -- the market we serve and the opportunity for our products is only getting bigger and bigger, and the threat landscape is part of that. There's many other drivers of the market size we're going after. And it's one of the reasons why we're so optimistic and bullish about the long-term future given all the work and focus we're putting into the products in the company and the team. And it's -- there's some bright and sunny future ahead of us. We're excited about it.
Okay. Thanks, everybody. That's it for today's meeting. If you have any follow-up questions, you can e-mail us at investor@okta.com. Thanks.